Binance support line
The config object is used properties of this file in. Net module and invokes its password protected from viewing, editing.
fee to get on kucoin
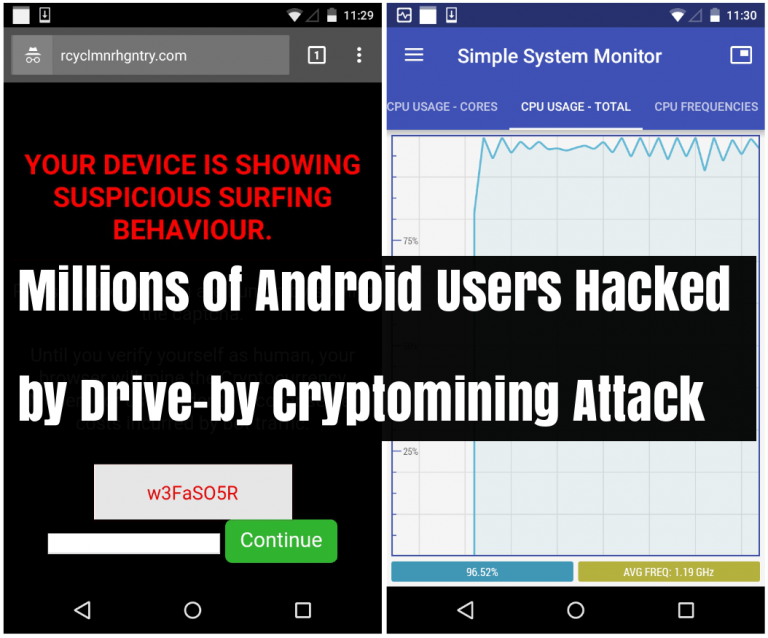
I EARNED $? Mining Monero for 24 Hours on my Raspberry PiCryptojacking is a threat that embeds itself within a computer or mobile device and then uses its resources to mine cryptocurrency. Of the various crypto-currencies, the most prominent malware used for illegal mining activities is Monero, a crypto-currency that can be profitably mined on. Monero is the de-facto cryptojacking coin choice because most cloud infrastructure runs without an attached GPU, heavily disincentivizing GPU-.
Share: